Rubrik, the Zero Trust Data Security Company™, delivers data security and operational resilience for enterprises.
Rubrik’s big idea is to provide data security and data protection on a single platform, including: Zero Trust Data Protection, ransomware investigation, incident containment, sensitive data discovery, and orchestrated application recovery. This means data is ready at all times so you can recover the data you need, and avoid paying a ransom. Because when you secure your data, you secure your applications, and you secure your business.

3 PILLARS OF RUBRIK ZERO TRUST DATA MANAGEMENT:
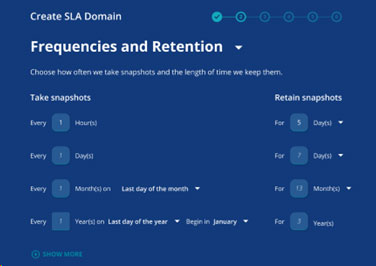
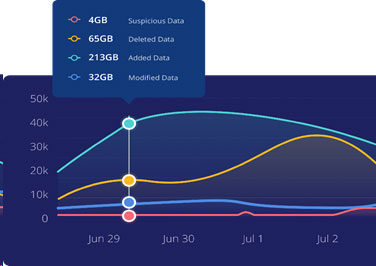
Identify scope of impact: See how your data has changed to quickly identify what was impacted where, allowing you to analyze the overall threat impact. By leveraging machine learning, you can detect and receive alerts on anomalous behavior, and quickly start the recovery process of your most critical applications. Use multiple recovery options to get your applications and data back to the most recent clean state.
Reduce sensitive data exposure: Identify whether any sensitive data has been breached and prioritize remediation plans with no impact to production. Create a robust compliance policy from a custom or pre-defined template, report on policy violations and track compliance progress.
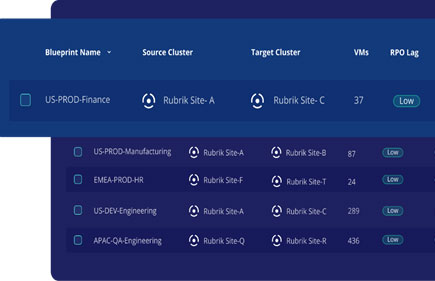
Accelerate ransomware recovery: Rubrik now takes ransomware recovery to the next level with fully orchestrated VM recovery to a secondary site or to VMware Cloud on AWS. Now you can define application blueprints ahead of time to ensure VMs get back online quickly and in the right sequence. With Enterprise Edition, Rubrik will help you secure your backup data and give you the essential tools to react to an attack.



3 PILLARS OF RUBRIK SECURITY CLOUD
Rubrik’s machine learning-based Security Cloud Management platform secures data in data centers, clouds and SaaS applications and offers automatic data protection against cyberattacks, continuous data risk monitoring and rapid recovery of data and applications.

Data Resilience
Secure your data from insider threats or ransomware with air-gapped, immutable, access-controlled backups:
– Intelligent Data Lock
– Retention Lock
– Access Control at Every Level
– Logical Air Gap
– Encryption Everywhere
– Immutable by Design
Data Observability
Continuously monitor your data for ransomware, remediate sensitive data exposure, and find indicators of compromise:
– Determine the scope of ransomware attacks, using high fidelity machine learning to detect deletion, modifications, and encryptions
– Reduce sensitive data exposure by discovering what types of sensitive data you have, where it lives, and who has access to it
– Prevent malware reinfection by analyzing the time-series history of snapshots for IOCs to identify initial point, scale, and time of infection
Data Remediation
Surgically and rapidly recover your apps, files or users, while avoiding
malware reinfection:
– Ensure safe and quick data recovery by quarantining
data infected with malware
– Restore business operations quickly by surgically recovering apps, files, or users
– Recover applications quickly with pre-built workflows
and disaster recovery plans